The Docker open-source platform has revolutionized the way we create, deploy, and manage containerized applications. To containerize an application, you’ll need to write a Dockerfile—which has instructions Docker uses for building and running images.
At times, you may need to set out some networking rules to enable smooth interaction between containers in multi-container applications or make your Docker ports accessible by services in the outside world.
You can do this in the following ways:
- Add an EXPOSE instruction in the Dockerfile
- Use the –expose flag at runtime to expose a port
- Use the -p flag or -P flag in the Docker run string to publish a port
Whereas each of the above rules may realize mostly similar results, they work differently.
So, which rule should you go for?
This article will demonstrate how to apply different networking rules when implementing Docker expose ports instructions in your code.
Exposing Docker ports via EXPOSE or –expose
There are two ways of exposing ports in Docker:
- Including an EXPOSE instruction in the Dockerfile
- Using the –expose flag at runtime
While the two commands are equivalent, they differ in how they work.
Let’s talk about each of them.
a) Using EXPOSE
With the EXPOSE rule, you can tell Docker that the container listens on the stated network ports during runtime.
Here is an example of how to expose a port in Dockerfile:
The above line will instruct Docker that the container’s service can be connected to via port 8080.
You can also expose multiple ports:
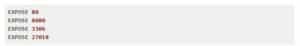
By default, the EXPOSE keyword specifies that the port listens on TCP protocol.
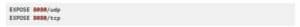
Here is how to expose on UDP:
If you want to specify both UDP and TCP, add two lines:
b) Using –expose
On the other hand, –expose is a runtime flag that lets you expose a specific port or a range of ports inside the container.
Using the flag is additive, which means that it will expose additional ports together with those stated by the EXPOSE keyword.
Here is an example of how to use the flag in a Docker run string:

You can also provide a range of ports as an argument:
How EXPOSE and –expose work
Basically, EXPOSE is a documentation mechanism that gives configuration information another command can use, provides a hint about which initial incoming ports will provide services, or informs the decisions that the container operator makes. EXPOSE does not provide much networking control to an image developer.
As earlier explained, you can use the –expose flag in a Docker run string to add to the exposed ports.
By default, the EXPOSE instruction does not expose the container’s ports to be accessible from the host. In other words, it only makes the stated ports available for inter-container interaction.
For example, let’s say you have a Node.js application and a Redis server deployed on the same Docker network. To ensure the Node.js application communicates with the Redis server, the Redis container should expose a port.
If you check the Dockerfile of the official Redis image, a line is included that says EXPOSE 6379. This is what allows the two containers to talk with one another.
Therefore, when your Node.js application connects to the 6379 port of the Redis container, the EXPOSE directive is what ensures the inter-container communication takes place.
Publishing Docker ports via -P or -p
There are two ways of publishing ports in Docker:
- Using the -P flag
- Using the -p flag
Let’s talk about each of them.
a) Using the -P flag
Using the -P (upper case) flag at runtime lets you publish all exposed ports to random ports on the host interfaces. It’s short for –publish-all.
As earlier mentioned, EXPOSE is usually used as a documentation mechanism; that is, hinting to the container operator about the port(s) providing services.
Docker allows you to add -P at runtime and convert the EXPOSE instructions in the Dockerfile to specific port mapping rules.
Docker identifies all ports exposed using the EXPOSE directive and those exposed using the –expose parameter. Then, each exposed port is mapped automatically to a random port on the host interface. This automatic mapping also prevents potential port mapping conflicts.
b) Using the -p flag
Using the -p (lower case) flag at runtime lets you publish a container’s specific port(s) to the Docker host. It’s short for –publish.
It allows you to map a container’s port or a range of ports to the host explicitly—instead of exposing all Docker ports.
Note that irrespective of the EXPOSE instructions in the Dockerfile, using the -p flag at runtime allows you to override them.
There are different formats for declaring the -p flag:
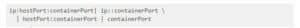
Here is how you can run it:

Basically, you may leave out either ip or hostPort references. However, you should always state the containerPort to expose. If ip or hostPort is left out, Docker will automatically provide them.
Furthermore, each of the publishing rules defaults to the TCP protocol. If you want UDP, you’ll need to specify it.
Here are some Docker expose port examples using the -p flag:

How publishing ports works
By default, if you use the docker run or docker create command to run or create a container, they do not make any Docker’s ports accessible by services in the outside world.
So, while it’s possible for your Docker containers to connect to the outside world without making any changes to your code, it’s not possible for the outside world to connect to your Docker containers.
If you want to override this default behavior, you can use either the -P or the -p flag in your Docker run string.
Publishing ports produce a firewall rule that binds a container port to a port on the Docker host, ensuring the ports are accessible to any client that can communicate with the host.
It’s what makes a port accessible to Docker containers that are not connected to the container’s network, or services that are outside of your Docker environment.
Differences between EXPOSE and publish
Whereas publishing a port using either -P or -p exposes it, exposing a port using EXPOSE or –expose does not publish it.
So, while exposed ports can only be accessed internally, published ports can be accessible by external containers and services.
That’s the main difference between exposing and publishing ports in Docker.
Conclusion
As we’ve demonstrated in this article, implementing various Docker expose ports scenarios during development is not difficult.
We hope you now understand how exposing ports, port binding, and other related concepts work in Docker.
Are you letting open-source vulnerabilities go undetected?
Mend Bolt is a powerful free extension that operates in real-time to provide visibility over your open source components within Azure Pipelines or GitHub.
- Get real-time alerts on security vulnerabilities
- Ensure the license compliance of open source components.
- Receive automated open-source inventory reports for every build or project.
Get it now and join thousands of developers who’ve already gained full visibility over their open-source components.