The sharp rise of reported open source vulnerabilities presents software development and security teams with new challenges. Teams can no longer fix all bugs and still meet tight development deadlines. Prioritizing security vulnerabilities is essential in order to focus limited remediation resources to resolve the most critical issues first.
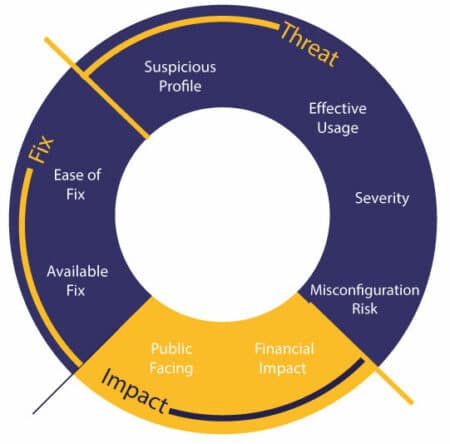
The default is to prioritize vulnerabilities based on easily accessible data like severity score, but this is not always the most effective way to remediate vulnerabilities and reduce your organization’s risk. Assessing the impact of a security vulnerability on an organization is complex work. In order to address the most immediate threats, organizations need to analyze a number of parameters.
Powerful Priority Scoring Saves Critical Remediation Resources
Mend Priority Scoring is an innovative approach that combines perceived risks from both security and non-security metrics. It is the first and only automated remediation solution to factor in business impact as part of overall vulnerability scoring.
A priority score between 0 and 100 is attributed to security issues by library or vulnerability. This score allows security teams to make informed decisions and implement automated risk-based policies so that the biggest overall threats to your business are remediated first.
Automatically Remediate Vulnerabilities Using Comprehensive Business Metrics
Effective Usage Analysis
Effective Usage Analysis is one of the parameters of Mend Priority Scoring. Effective Usage Analysis technology scans open source components with known vulnerabilities to assess whether your proprietary code is making calls to the vulnerable method, making it effective.
Our research shows that only 15% to 30% of vulnerabilities are indeed effective, so your team can easily focus on remediating the vulnerabilities that matter the most.
Prioritize Based on Effectiveness
Vulnerability effectiveness level is displayed with shield icons.
The summary pane displays the number of libraries analyzed, their severity, and how many are effective.
The Analysis Statistics section at the bottom displays the percentage of libraries analyzed, and the number of effective and non-effective security alerts.
Optimize Remediation Processes
- When an effective vulnerability is identified, a detailed call graph presents the complete paths from the proprietary code to the vulnerable functionality.
- This pinpoints the exact location of the vulnerable functionality and the path that leads to it.
- The call graph shows developers where a reference occurs, including filename, class name, and line in the code.
- These details considerably shorten review and remediation time, saving precious resources and helping organizations fix their critical vulnerabilities faster.

Learn More
Discover how Mend SCA helps simplify the management of open source components in your software.